 As a Windows systems administrator, there are plenty of situations where you need to remotely view who is logged on to a given computer. Many times you not only need to check who is logged on interactively at the console, but also check who is connected remotely via a Remote Desktop Connection (RDP). Fortunately Windows provides a way to do this. In fact, there are at least three ways to remotely view who’s logged on.
As a Windows systems administrator, there are plenty of situations where you need to remotely view who is logged on to a given computer. Many times you not only need to check who is logged on interactively at the console, but also check who is connected remotely via a Remote Desktop Connection (RDP). Fortunately Windows provides a way to do this. In fact, there are at least three ways to remotely view who’s logged on.
Each of these methods for remotely viewing who is logged on to a Windows machine assumes your Windows login has sufficient permission to connect remotely to the machine. It’s also worth pointing out that each of these ways is non-invasive. This means you can use them to check on the given machine remotely without impacting any of the users currently logged on to the remote machine.
Remote Desktop Services Manager
The Remote Desktop Services Manager is part of the Remote Server Administration Tools (RSAT) suite of tools, so you’ll need to install RSAT before you can use the Remote Desktop Manager. We also touched on the Remote Desktop Services Manager in our article about how to manage remote desktop connections.
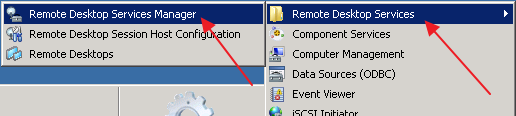
After you have RSAT installed with the “Remote Desktop Services Tools” option enabled, you’ll find the Remote Desktop Services Manager in your Start Menu, under Administrative Tools, then Remote Desktop Services:
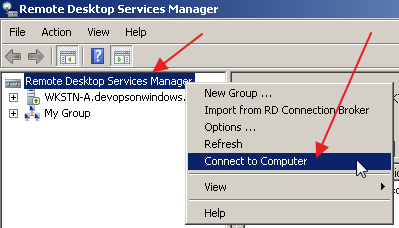
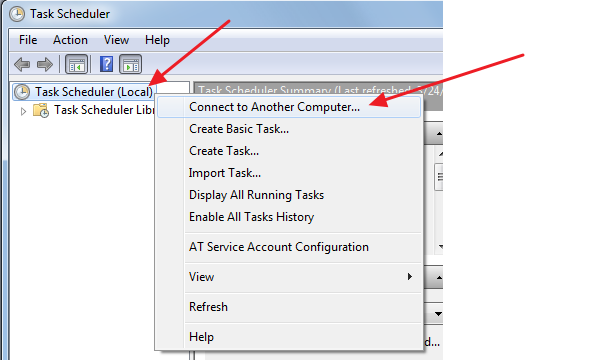
Once the Remote Desktop Services Manager MMC is up and running, simply right click on the “Remote Desktop Services Manager” root node in the left pane tree view:
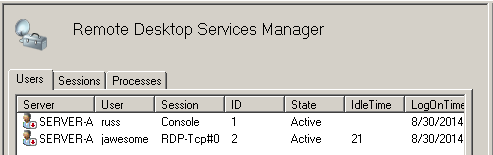
Then when prompted, enter the hostname of the remote computer you want to view. After the MMC connects to the remote computer, you’ll see a list of users logged on to the machine and which session they’re each using:
PsLoggedOn
If you’ve read some of our previous articles you know that we’re big fans of the SysInternals suite of system utilities. Included in the PsTools set of utilities is a handy little command line app, PsLoggedOn.
As with other SysInternals tools, you’ll need to download psloggedon.exe and place it somewhere accessible on your local computer (not the remote computer), for example, in C:\PsTools.
Then, open a command prompt on your local machine and from any directory execute: C:\PsTools\psloggedon.exe \\server-a
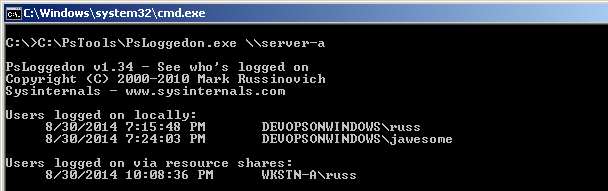
This of course assumes you put psloggedon.exe in C:\PsTools on your local machine, and replace “server-a” with the hostname of the computer you want to remotely view who is logged on.
Query
Last but not least, there’s the built-in Windows command, “query”, located at %SystemRoot%\system32\query.exe.
Just open a command prompt and execute: query user /server:server-a
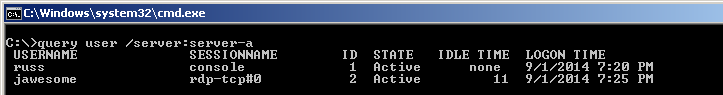
As usual, replace “server-a” with the hostname of the computer you want to remotely view who is logged on.
For more information on the query command see http://support.microsoft.com/kb/186592
As you can see there are at least three ways to get the information you need to remotely view who is logged on in a totally non-intrusive way.


Another cool set of similar commands are qwinsta and rwinsta. qwinsta queries the users similar to the ‘query user’ command, and rwinsta is utilized to remove the session (by session ID revealed in qwinsta).
Thanks Jeff!
What if the network you are trying to reach requires different credentials than your PC’s logon credentials? Is there a way to supply username+password, similar to the way “Tools | Map Network Drive … ” does in Windows Explorer? The only way I have found is to use Remote Desktop to log onto another PC on the target network, and then to use one of the solutions you listed from the remote PC.
type this at command prompt
cmdkey /?
Hi Mitch!
You should be able to use one of the User Impersonation techniques described in https://devopsonwindows.com/user-impersonation-in-windows/ (e.g. shift+right click, runas command, etc.) to launch one of the above tools (Remote Desktop Services manager, PsLoggedOn, etc.) using a different username and password (i.e. the user that has access to the remote machine you’re checking on) on/from your local machine directly.
Hope that helps!
Hi Russ. That works great!
Thanks!
mkdir %username%
pushd %username%
@echo off
echo
echo I am logged on as %UserName%. >> %username%\%computername%.txt
echo My computer’s name is %ComputerName%. >> %computername%.txt
echo %Date% >> %computername%.txt
echo %Time% >> %computername%.txt
echo My IP settings are >> %computername%.txt
ipconfig | find “.” | find /i /v “suffix” >> %computername%.txt
getmac >> %computername%.txt
echo\
this can export the full information
worked great thanks,
is there a way i can use this tool to see the log history for the past week for example ?
Will it work on WinXP?
Turning this into a batch file that prompts for the remote computer name:
@echo off
@echo Remote query logged in user of specified computer. Requires Sysinternals psloggedon
:BEGIN
set /P remotecomputer=Enter computer name to query logged in user, and press ENTER:
set servicename=remoteregistry
if [%remotecomputer%] == [] GOTO BEGIN
@REM start %servicename% service if it is not already running
for /F “tokens=3 delims=: ” %%H in (‘sc \\%remotecomputer% query %servicename% ^| findstr ” STATE”‘) do (
if /I “%%H” NEQ “STOPPED” (
sc \\%remotecomputer% config remoteregistry start= demand
sc \\%remotecomputer% start remoteregistry
)
)
@rem query user /server:%remotecomputer%
@rem wmic.exe /node:”%remotecomputer%” computersystem get username
psloggedon.exe \\%remotecomputer%
GOTO BEGIN
This PowerShell script works for me all the time. Run this on PowerShell console
Full command:
Get-WmiObject Win32_ComputerSystem -ComputerName | Format-List Username
Shorten command:
gwmi Win32_ComputerSystem -cn | fl username
Hope you’d like it 🙂
I like the query command. thanks!
A fourth method, using a native Windows command:
tasklist /s computername /fi “imagename eq explorer.exe” /v
You may be prompted for admin-level credentials when querying a remote machine.
This will see if explorer.exe (the Desktop environment) is running on a machine, and “/v” provides the username. If a machine is not logged in, no explorer.exe process will be running. If someone is logged on, the explorer.exe process runs in the context of that user.
Amazing. Thanks
Is there a way for non admin user to query the remote machine to check user access to the machine. The non admin user don’t have access to the remote machine but he is part of the network
Hi guys, I need to count the total users logged on the server, but the “query user /server” shows all logged users.
Is there a way to use “|” how to count the total “username” and show the number?
Greetings from six years in the future. This post and the comments are very helpful. Thanks!